Truecrypt is available as a Red Hat/CentOS package on RPMForge, however I found that it's problematic and only supports FAT disks. I needed to use Truecrypt to encrypt a USB drive that is going to store files larger than 4GB so FAT isn't an option.
There's many conflicting accounts on various forums on how to compile Truecrypt on CentOS 5 however the most helpful was still the README provided in the source package which still required a bit of trial and error to get a working binary at the end.
Therefore here's my walkthrough on the quickest, simplest way to get Truecrypt 6.1 compiled and working on a vanilla CentOS 5 installation.
Therefore here's my walkthrough on the quickest, simplest way to get Truecrypt 6.1 compiled and working on a vanilla CentOS 5 installation.
Switch user to root.
su -
** UPDATE - RPMForge was merged into RPMFusion which also requires the EPEL repo on RHEL/CentOS**
Firstly setup access to the EPEL repositories, download the latest EL5 RPM from their repo. This package just installs the EL5 repo file and the required GPG keys, install it with;
The RPMFusion repository provides decent packages for fuse and wxwidgets which are required by Truecrypt, this really simplifies the process as I found setting up wxwidgets & fuse from source to be a chore.
rpm -i /pathtoyour/epel-release-5??.noarch.rpm
The RPMFusion repository provides decent packages for fuse and wxwidgets which are required by Truecrypt, this really simplifies the process as I found setting up wxwidgets & fuse from source to be a chore.
Upto date instructions for enabling this repo is at rpmfusion.org/Configuration, the correct command-line for downloading & installing free & nonfree RPMFusion repos at time of writing is;
rpm -Uvh http://download1.rpmfusion.org/free/el/updates/5/i386/rpmfusion-free-release-5-1.noarch.rpm http://download1.rpmfusion.org/nonfree/el/updates/5/i386/rpmfusion-nonfree-release-5-1.noarch.rpm
Once RPMFusion is setup then install the following packages and their dependencies;
yum install gcc gcc-c++ gnome-keyring-devel kernel-devel kernel-headers wxGTK wxGTK-devel fuse fuse-devel fuse-ntfs-3g
Next download the Mac OSX/Linux source package from the Truecrypt website at http://www.truecrypt.org/downloads2.php and save it somewhere. In this example I've saved it to /tmp.
Now in a terminal goto the location of the archive and unpack it.
cd /tmp
tar xvfz “TrueCrypt 7.1a Source.tar.gz”
... cd to the new directory containing the extracted source code
cd truecrypt-7.1a-source
Download the RSA Cryptoki 2.20 header files required by Truecrypt into the source directory.
wget ftp://ftp.rsasecurity.com/pub/pkcs/pkcs-11/v2-20/*.h
Compile Truecrypt.
*UPDATE: Include the NOASM flag to prevent assembly with nasm*
*UPDATE: Include the NOASM flag to prevent assembly with nasm*
make NOASM=1
The compilation process should now breeze through with no errors.
Now copy the compiled binary to /usr/bin
cp -p Main/truecrypt /usr/bin/
chmod +x /usr/bin/truecrypt
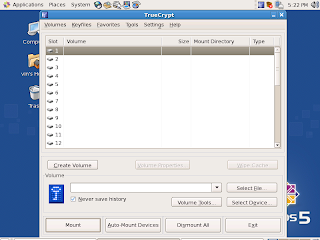
You can now start Truecypt from a root terminal.
truecrypt
Swapping encrypted disks between Linux & Windows systems
My requirement for Truecrypt on CentOS was for transporting sensitive data on an encrypted USB hard disk to one of our software suppliers. The guys receiving the data run Windows on their systems whereas we run HP-UX, RHEL & CentOS on our systems, Truecrypt was the only decent open-source cross-platform solution that would enable us to securely transport the encrypted data without it being too technical for the guys receiving it.
However I was a bit disappointed with how different the Windows version was to the Linux version and it became apparent that the project still needs some direction in terms of enhancing the cross-platform nature of Truecrypt.
One area where this was apparent was the filesystem options available in the GUI, the Windows version only had options to create or mount FAT32 & NTFS encrypted filesystems whereas the Linux version only had options for FAT32, Ext3 & Ext2 filesystems.
However I was a bit disappointed with how different the Windows version was to the Linux version and it became apparent that the project still needs some direction in terms of enhancing the cross-platform nature of Truecrypt.
One area where this was apparent was the filesystem options available in the GUI, the Windows version only had options to create or mount FAT32 & NTFS encrypted filesystems whereas the Linux version only had options for FAT32, Ext3 & Ext2 filesystems.
If you intend to swap an encypted disk with large file support between Linux & Windows platforms, it is not possible to do this by using the Truecrypt GUIs alone.
After some time testing the best solution for this was to use a NTFS filesystem on the USB disk and encrypt the whole filesystem on a Windows platform using the GUI.
When it comes to using the encrypted disk on the Linux platform you have to mount and dismount it with Truecrypt's command-line options as the GUI does not support this.
After some time testing the best solution for this was to use a NTFS filesystem on the USB disk and encrypt the whole filesystem on a Windows platform using the GUI.
When it comes to using the encrypted disk on the Linux platform you have to mount and dismount it with Truecrypt's command-line options as the GUI does not support this.
Examples
To mount the encrypted NTFS volume on Linux;
As root substituting the 'correctpassword', the device path & the mountpoint as appropriate...
As root substituting the 'correctpassword', the device path & the mountpoint as appropriate...
truecrypt -t --filesystem=ntfs-3g -k "" --protect-hidden=no --fs-options=user,users,gid-users,umask=0002 -p correctpassword /dev/sdx1 /pathto/mountpoint
To unmount the encrypted volume;
As root...
As root...
truecrypt -t -d /dev/sdx1
or...
truecrypt -d /pathto/mountpoint
What doesn't work?
- Truecrypt on Windows will not mount an encrypted Ext2 or Ext3 filesystem, even with an appropriate Ext filesystem driver installed.
- Truecrypt on Linux will not mount an encrypted file container, mounting a file residing on an already mounted filesystem seems to be the problem.
- The Linux Truecrypt GUI cannot gain elevated privileges after entering your sudo password, even if sudo/sudoers is setup correctly, therefore su to root before executing the GUI from a terminal.
- The Truecrypt GUI on Linux cannot mount encrypted NTFS filesystems